Cybersecurity & Data Sovereignty: Global-Level Protection
Data in Motion, Security at Rest
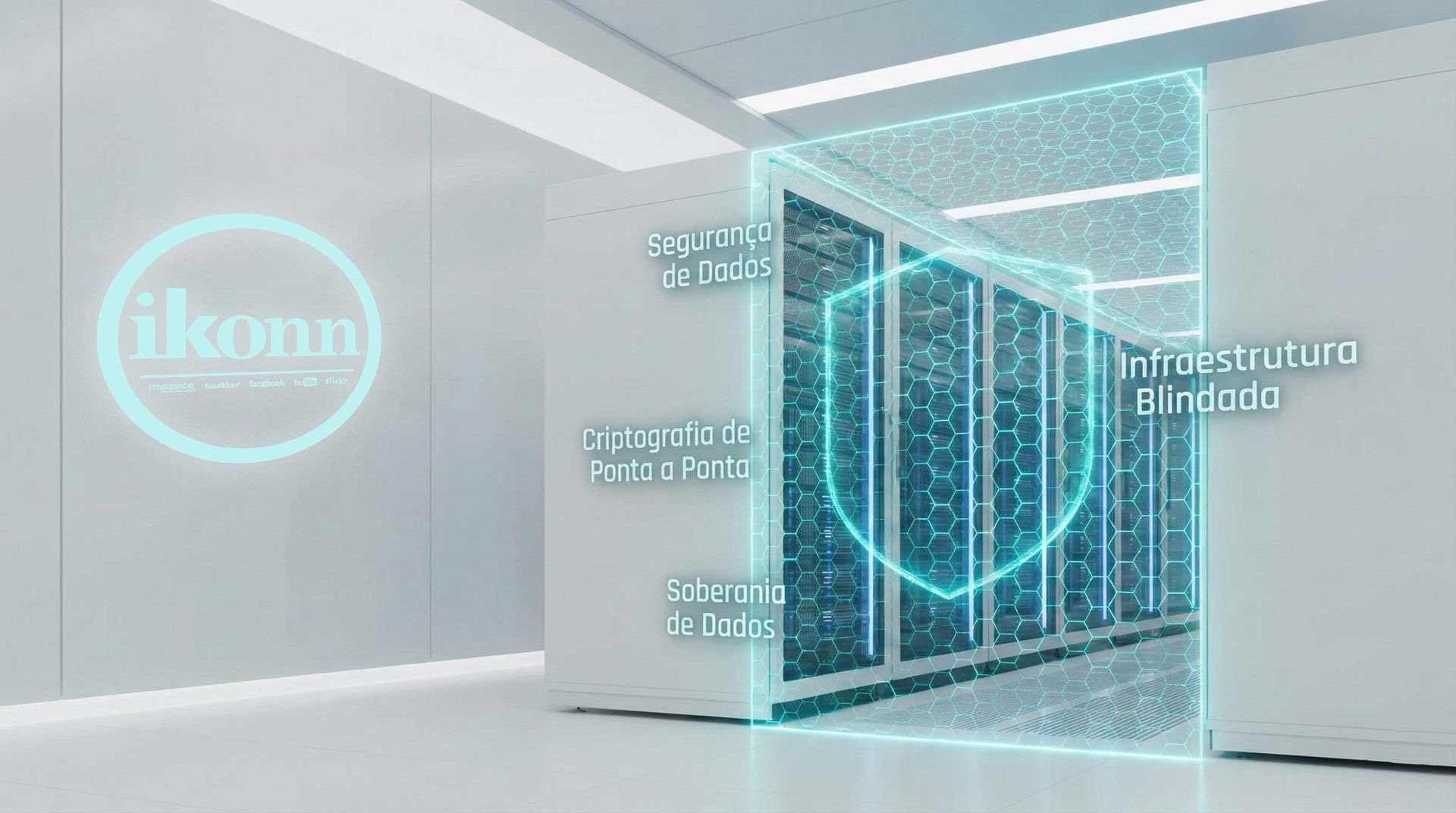
In an era of sophisticated cyberattacks and constant data leaks, information security has gone from being a differentiator to becoming the cornerstone of any serious tracking center. At Ikonn , we treat every GPS coordinate and every telemetry alert as a critical asset. The concept of Cybersecurity & Data Sovereignty permeates all our engineering, ensuring that your operation is protected against external threats and structural failures.
Our architecture doesn't just store data; it protects it. We use high-level encryption protocols to ensure that communication between the IoT device, the server, and your client's application is completely private and inviolable.
Tier IV Infrastructure and High Availability
Where your data resides matters. Ikonn operates in Tier IV certified data centers, the highest standard of redundancy and availability in the world. This means that its data center has fault-tolerant power, cooling, and connectivity systems, guaranteeing uptime exceeding 99.99%.
- Geographic Redundancy: Your data is replicated across multiple global locations, ensuring rapid recovery in the event of natural disasters or regional failures.
- Proactive Monitoring: Our security team operates 24/7 with intrusion detection systems and real-time DDoS attack mitigation.
- Compliance with the LGPD: Native tools for privacy and consent management, ensuring your company is 100% compliant with the General Data Protection Law.
Data Sovereignty: You Are the Owner
One of the biggest risks of rigid platforms is "data lock-in." At Ikonn, we believe in Data Sovereignty . This means that while we provide the technology and infrastructure, you are the intellectual owner of your data center.
We offer complete freedom to export information and integrate via secure APIs, allowing you to connect your database to external Business Intelligence (BI) systems or customized ERPs. Your company maintains strategic control, while we provide technical security.
Privacy as a Selling Point
Conveying security to the end customer is one of the most powerful closing arguments your team can have. When you use Ikonn technology, you give your customer the peace of mind of knowing that their family's journey or the location of their multi-million dollar fleet is not vulnerable to hackers or unauthorized access.
Ikonn's security is invisible to the user, but it's felt in the application's stability and the absolute integrity of every generated report. It's the prestige of security engineering serving your brand's reputation.
Conclusion: Resilience in a Connected World
Cybersecurity is not a destination, it's a continuous process of adaptation. By choosing Ikonn, you join a platform that invests heavily in digital defense research to anticipate tomorrow's threats. Protect your legacy, shield your operations, and ensure your customers' trust with the data sovereignty that only Ikonn offers.
In security, there's no middle ground. Demand data engineering from Ikonn.
Do you need a secure infrastructure for your control center?
Talk to our security experts and discover how we protect the future of your business.